Standoff as IEBC grants access to only one of its 8 servers despite Supreme Court order
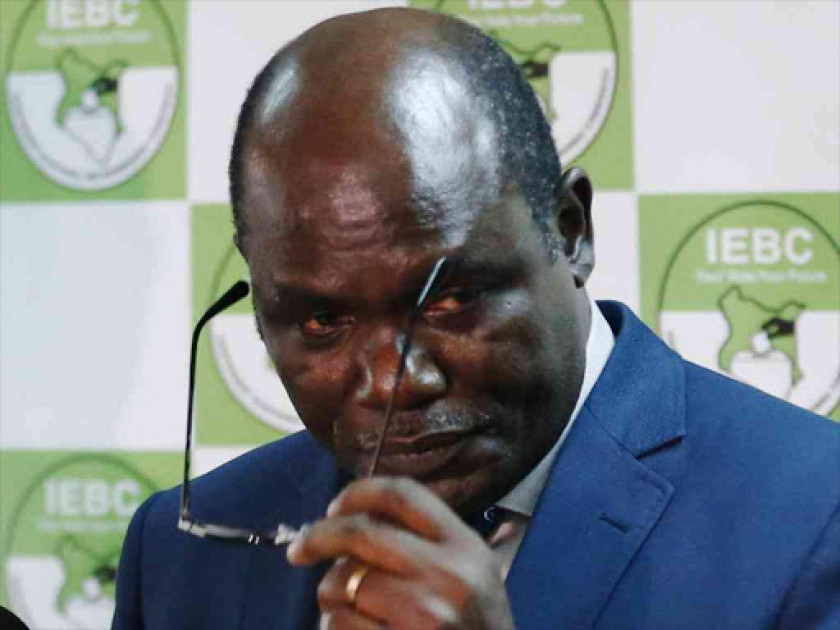
IEBC Chairperson Wafula Chebukati. | FILE

Audio By Vocalize
There was a stand-off at the Independent Electoral and
Boundaries Commission (IEBC) headquarters in Nairobi on Wednesday after the
commission refused to give access to its servers per a Supreme Court directive.
The Supreme Court granted Raila Odinga access
to the technology used in transmitting results at the IEBC National Tallying
Centre at Bomas of Kenya in Nairobi.
According to Senior Counsel James Orengo, the
commission however gave restricted access to only one of its eight servers.
“We have been given restricted access only to
the result transmission system, and it has not been granted yet, to only one
server. It is established that the IEBC has eight servers,” Orengo told the
court in his submission shortly after the hearing resumed at 2pm.
Orengo told the seven-member bench led by
Chief Justice Martha Koome that they had written to the Judiciary registrar
Anne Amadi over the issue and prayed that the court intervene.
"We have written to the registration so
that the court can resolve this," he said.
In response, Supreme Court judge Isaac Lenaola
noted that the court was aware of the issue and was following up.
“We are aware and
we are following it up. As far as we know
when we got out of here, the exercise had commenced, there was an agreement on
how to access the server that had been given,” said Justice Lenaola.
“The issue of cloning is being addressed and
we will report on the issue again tomorrow morning.”
IEBC was on Tuesday ordered to provide supervised access to
any server used to capture images of Forms 34C at the commission's nerve centre
during a Pre-Trial conference on the presidential election petition.
"That IEBC be compelled to give the
applicants supervised access to any server(s) at the National Tallying Centre
for storing and transmitting voting information and which are forensically
imaged to capture a copy of the Form 34C which is the total votes cast,"
read court documents.
The court also ordered IEBC to provide copies of its technology system security policy, which included their password policy, password matrix, and system administration password owners.

Join the Discussion
Share your perspective with the Citizen Digital community.
No comments yet
This discussion is waiting for your voice. Be the first to share your thoughts!